Prepare ArgoCD
ArgoCD is the GitOps engine Red Hat OpenShift GitOps rely on. It should have been installed previously in Deploying core components.
Checking ArgoCD
Once ArgoCD has been rolled out, this is something that should have been done by someone with enough permissions, you can run this simple test.
| You should get something like this. If you don’t, be patient and run this command in 2 mins or so. |
HTTP/1.1 200 OK
set-cookie: i_like_gitea=82e42fd387b6ea7a; Path=/; HttpOnly; SameSite=Lax
date: Mon, 25 Oct 2021 08:06:22 GMT
set-cookie: 5b3fc896c2f6eedc568a6b59cd1862ea=23d42cb20150039ef52136e8993c6865; path=/; HttpOnly; Secure; SameSite=None
cache-control: privateLog in ArgoCD with CLI
Well ArgoCD is healthy now let’s see if the CLI works correctly by trying to log in with it (you should have installed as stated in Prerequisites section).
|
You’ll be redirected to OpenShift Web Console to enter your credentials:
|
argocd login openshift-gitops-server-openshift-gitops.apps.%BASE_SUBDOMAIN% --insecure --sso --grpc-webexport ARGOCD_HOST=$(oc get route/openshift-gitops-server -o jsonpath='{.status.ingress[0].host}' -n openshift-gitops)
export ARGOCD_USERNAME=admin
export ARGOCD_PASSWORD=$(oc get secret openshift-gitops-cluster -o jsonpath='{.data.admin\.password}' -n openshift-gitops | base64 -d)
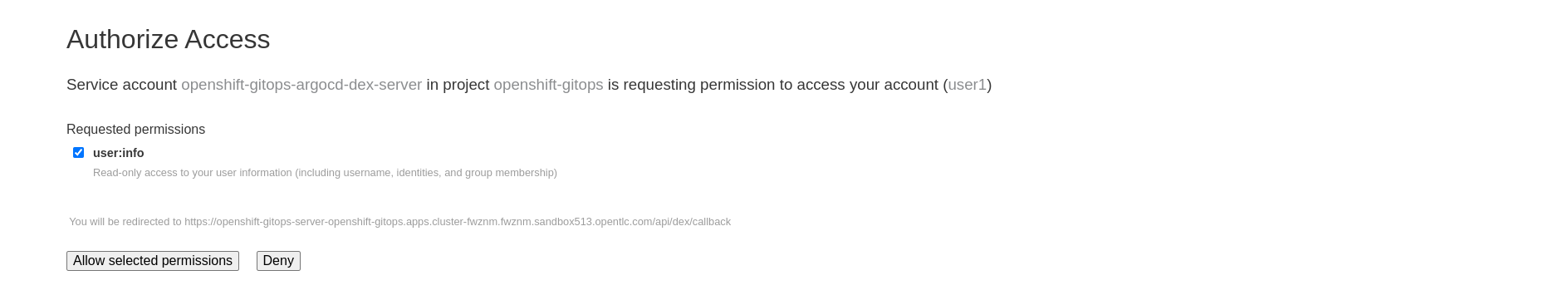
argocd login $ARGOCD_HOST --insecure --grpc-web --username $ARGOCD_USERNAME --password $ARGOCD_PASSWORDYou may see this message, if that is the case click on Allow selected permissions and continue.
After being successfully logged in, you should be redirected to localhost:8085 with a message of successful authentication and in the terminal output you should see something similar to this.
Opening browser for authentication
Performing authorization_code flow login: https://openshift-gitops-server-openshift-gitops.apps.%BASE_SUBDOMAIN%/api/dex/auth?access_type=offline&client_id=argo-cd-cli&code_challenge=VVX5Feb1ySsRQAUNfvSrolTt8yak2HKjUZ-YjuQgItI&code_challenge_method=S256&redirect_uri=http%3A%2F%2Flocalhost%3A8085%2Fauth%2Fcallback&response_type=code&scope=openid+profile+email+groups+offline_access&state=zsQHLaywsv
Authentication successful
'%USERNAME%' logged in successfully
Context 'openshift-gitops-server-openshift-gitops.apps.%BASE_SUBDOMAIN%' updatedRegister Repositories
In this guide we cover the case of a protected git repository that needs to be interacted with from a system and you don’t want your personal password to be exposed that’s why you have created a Personal Access Token.
argocd --insecure repo add https://repository-gitea-system.apps.%BASE_SUBDOMAIN%/%USERNAME%/gramola.git --username %USERNAME% --password ${GIT_PAT} --upsert --insecure-skip-server-verification --grpc-webRun this command to list the registered repositories.
argocd --insecure repo list --grpc-webThis is a typical response.
TYPE NAME REPO INSECURE OCI LFS CREDS STATUS MESSAGE
git https://repository-gitea-system.apps.%BASE_SUBDOMAIN%/user1/gramola.git false false false true SuccessfulRegister Additional Clusters[1]
First make sure there is a context with proper credentials, in order to achieve this please log in the additional cluster.
| ADDITIONAL_API_SERVER_TOKEN is a token of a user with cluster-admin permissions on the additional cluster, ADDITIONAL_API_SERVER_MANAGED is the host and port without http(s) of the additional cluster. |
export ADDITIONAL_API_SERVER_TOKEN=%ADDITIONAL_API_SERVER_TOKEN%
export ADDITIONAL_API_SERVER_MANAGED=api.%ADDITIONAL_BASE_SUBDOMAIN%:6443
oc login --token=${ADDITIONAL_API_SERVER_TOKEN} --server=https://${ADDITIONAL_API_SERVER_MANAGED}Give a name to the additional cluster and add it with the next command.
| CLUSTER_NAME is a name you choose for your cluster. |
export CLUSTER_NAME=aws-managed1
CONTEXT_NAME=$(oc config get-contexts -o name | grep ${ADDITIONAL_API_SERVER_MANAGED})
argocd --insecure cluster add ${CONTEXT_NAME} --name ${CLUSTER_NAME} --grpc-web
You will see the following message warning you that if you proceed you will create a ServiceAccount called argocd-manager with full cluter lever admin privileges. Don’t worry and please type y and press Enter.
|
WARNING: This will create a service account `argocd-manager` on the cluster referenced by context `default/api-cluster-...opentlc-com:6443/opentlc-mgr` with full cluster level admin privileges. Do you want to continue [y/N]? yCheck if your cluster has been added correctly.
argocd --insecure cluster list --grpc-webThis is the expected output:
SERVER NAME VERSION STATUS MESSAGE PROJECT
https://api.cluster-...opentlc.com:6443 aws-managed1 Unknown Cluster has no application and not being monitored.
https://kubernetes.default.svc in-cluster 1.23 SuccessfulNow, it’s time to log back in the main cluster.
oc login -u %USERNAME% -p %PASSWORD% --server=https://api.%BASE_SUBDOMAIN%:6443Project definitions
In ArgoCD you can constrain which repositories and destinations can be linked with the definition of an application, in our case we are not constraining but we still have created project definitions to be prepared for future needs.
Run this command to see the list of project definitions.
argocd --insecure proj list --grpc-webThis is the expected result, one project definition for development and another one for testing.
NAME DESCRIPTION DESTINATIONS SOURCES CLUSTER-RESOURCE-WHITELIST NAMESPACE-RESOURCE-BLACKLIST SIGNATURE-KEYS ORPHANED-RESOURCES
default *,* * */* <none> <none> disabled
gramola-project-dev Gramola Project Dev *,* * */* <none> <none> disabled
gramola-project-test Gramola Project Test *,* * */* <none> <none> disabled